Retailers, the hotel and restaurant industry, health care, administrative institutions, and educational and research institutions in particular are targeted by malware with a corona theme, according to ‘Bitdefender Labs’.
Cyber criminals have started to use the pandemic for their own purposes. They take advantage of people’s concerns about increased information needs, thereby spreading malware, phishing emails and operating general online fraud.
The latest Bitdefender telemetry shows a rapid increase in the cyber threats associated with the coronavirus: the number of malware reports relating to coronavirus rose to no less than 475 percent in the middle of the month in March compared to February as a whole - from 1,448 to 8,319 reports.
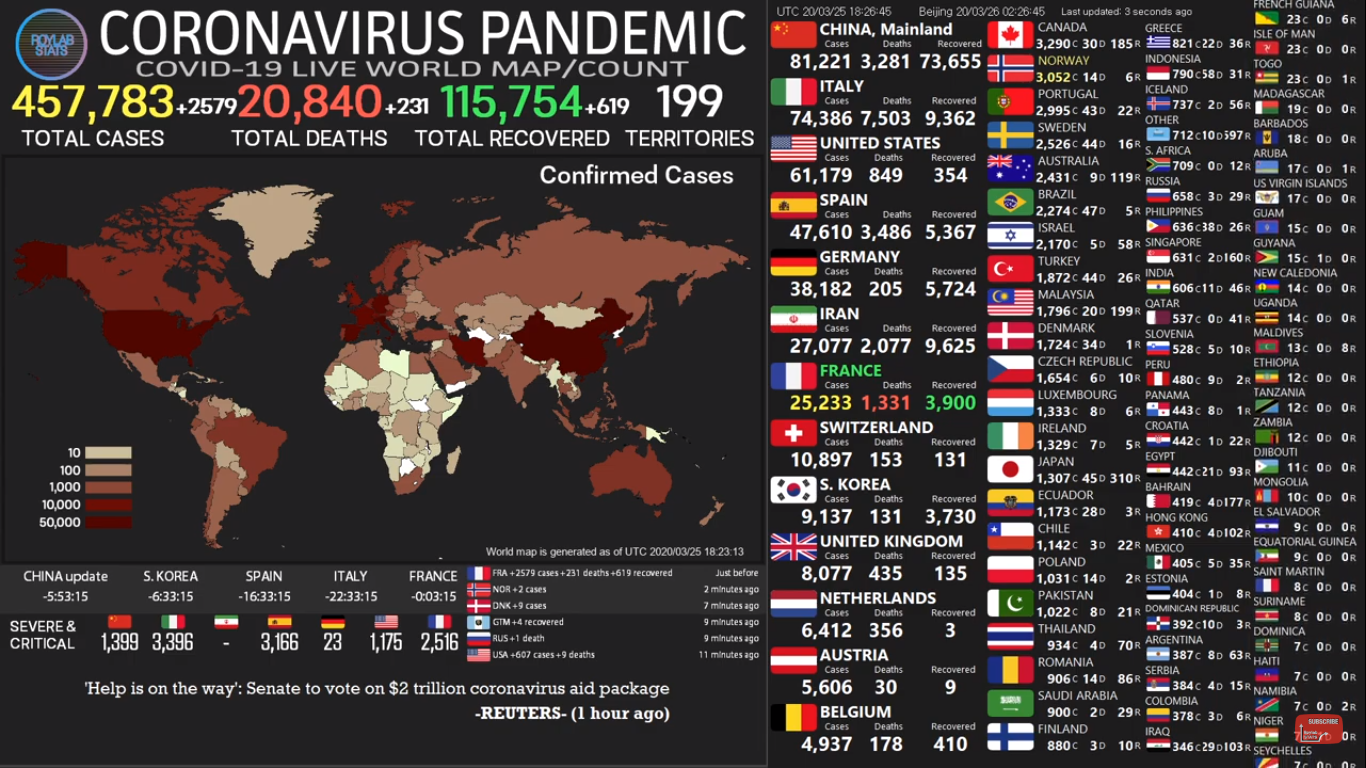
(3/25/2020, Youtube: Roylab Stats | https://www.youtube.com/watch?v=SLV1B5Lzy48 )
The public sector, retail, hospitality, transport, education and research seem to be most affected. These sectors are targeted because they actively interact with large groups of people and are the ones who have the greatest interest in the necessary measures to fight pandemics. Cybercriminals are massively approaching these industries with phishing emails, pretending to be WHO, NATO and UNICEF - institutions from which employees expect official information.
Common denominator: Coronavirus
If you look at some of the infected documents, all filenames have the same string “corona virus” and promise to provide new and exclusive information. It is often claimed that the email attachments are PDF documents, even though they are an “.exe” or “.bat” file. Users who have not activated the “File name extensions” option in the File Explorer view often fall prey to this double-extension scam. These files are infiltrated with malware and spread various threats. Most of these Trojans, including NanoBot, are designed to steal personal information like usernames and passwords. Hackers can use them for remote access to accounts, services and end devices.
All European countries are affected
The situation escalated between January and March. In January, reports came from only a few countries, such as the United States, China and Germany. In March, malware reports came from all over the world. No European country was spared. The digital threat actors exploited uncertainty, misinformation and confusion to benefit as much as possible from the current situation.